Known Exploited Vulnerabilities Catalog
Known Exploited Vulnerabilities Catalog - Cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild and recommends prioritizing their remediation. Browse the latest updates for apple, microsoft, sonicwall, linux, and other products, and see. Learn how to use the kev. Cisa provides the so called known exploited vulnerabilities catalog (kev) which contains information about security issues, that have been exploited in the wild and does therefore. The known exploited vulnerability (kev) catalog, maintained by cisa, is the authoritative source of vulnerabilities that have been exploited in the wild. Learn how cisa's known exploited vulnerabilities (kev) catalog helps organizations prioritize and address actively exploited security risks for robust cyber defense. Vuldb provides enhanced details and quality of cisa's known exploited vulnerabilities catalog (kev), which contains information about security issues that have been. In january 2025, fourteen vulnerabilities met the criteria for inclusion in the cisa’s kev catalog. Automates it operationszero trust network accessenable frictionless work Cisa has added three new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. Cisa has added three new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. With that understanding, we launched the known exploited vulnerabilities catalog (known simply as “the kev ”) in november 2021 to provide an authoritative source of. The known exploited vulnerability (kev) catalog, maintained by cisa, is the authoritative source of vulnerabilities that have been exploited in the wild. Shadowserver disclosed evidence of 31 actively exploited vulnerabilities, followed by. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa. The nvd provides a text reference and a hyperlink to the kev catalog for cves that appear in it. Learn how to use the kev. Cisa provides the so called known exploited vulnerabilities catalog (kev) which contains information about security issues, that have been exploited in the wild and does therefore. The flaws were added yesterday to cisa's 'known exploited vulnerabilities' (kev) catalog, with the broadcom brocade fabric os and commvault flaws not previously tagged as. Browse the latest updates for apple, microsoft, sonicwall, linux, and other products, and see. Cisa strongly recommends organizations to remediate the vulnerabilities in the catalog to. The known exploited vulnerability (kev) catalog, maintained by cisa, is the authoritative source of vulnerabilities that have been exploited in the wild. Four have been exploited by known threat actors. This vulnerability allows remote attackers to inject. The disclosure of known exploited vulnerabilities was from 50. Learn how cisa's known exploited vulnerabilities (kev) catalog helps organizations prioritize and address actively exploited security risks for robust cyber defense. Learn how to use the kev. Cisa strongly recommends organizations to remediate the vulnerabilities in the catalog to. Cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild. This vulnerability allows remote attackers to inject. In q1 2025, vulncheck identified evidence of 159 cves publicly disclosed for the first time as exploited in the wild. The catalog is maintained by cisa, which is a government agency responsible for. Vulncheck also named the top sources of exploitation evidence during the quarter. Cisa provides the so called known exploited vulnerabilities catalog (kev) which contains information about security. Shadowserver disclosed evidence of 31 actively exploited vulnerabilities, followed by. Cisa provides the so called known exploited vulnerabilities catalog (kev) which contains information about security issues, that have been exploited in the wild and does therefore. Learn how cisa's known exploited vulnerabilities (kev) catalog helps organizations prioritize and address actively exploited security risks for robust cyber defense. Vulncheck also named. Cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild and recommends prioritizing their remediation. Vulnerability in best practical solutions, llc's request tracker v5.0.7, where the triple des (3des) cryptographic algorithm is used within smime code to encrypt s/mime emails. This web page provides a printable version of the cisa known exploited vulnerabilities catalog, which lists. Cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild. The disclosure of known exploited vulnerabilities was from 50. Cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild and recommends prioritizing their remediation. The nvd provides a text reference and a hyperlink to the kev catalog for cves that appear in. The nvd provides a text reference and a hyperlink to the kev catalog for cves that appear in it. The catalog is maintained by cisa, which is a government agency responsible for. In q1 2025, vulncheck identified evidence of 159 cves publicly disclosed for the first time as exploited in the wild. Cisa has added 15 new vulnerabilities to its. Cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild and recommends prioritizing their remediation. Four have been exploited by known threat actors. Vulnerability in best practical solutions, llc's request tracker v5.0.7, where the triple des (3des) cryptographic algorithm is used within smime code to encrypt s/mime emails. Vulncheck also named the top sources of exploitation. This vulnerability allows remote attackers to inject. Four have been exploited by known threat actors. Learn how to use the kev. The nvd provides a text reference and a hyperlink to the kev catalog for cves that appear in it. Cisa strongly recommends organizations to remediate the vulnerabilities in the catalog to. The disclosure of known exploited vulnerabilities was from 50. The catalog is maintained by cisa, which is a government agency responsible for. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa. This vulnerability allows remote attackers to inject. The flaws were added yesterday to cisa's 'known. Four have been exploited by known threat actors. Cisa strongly recommends organizations to remediate the vulnerabilities in the catalog to. Cisa has added 15 new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence that threat actors are actively exploiting the vulnerabilities listed in. The catalog is maintained by cisa, which is a government agency responsible for. Learn how cisa's known exploited vulnerabilities (kev) catalog helps organizations prioritize and address actively exploited security risks for robust cyber defense. This web page provides a printable version of the cisa known exploited vulnerabilities catalog, which lists cves for various products and vendors that are known to. This vulnerability allows remote attackers to inject. With that understanding, we launched the known exploited vulnerabilities catalog (known simply as “the kev ”) in november 2021 to provide an authoritative source of. In january 2025, fourteen vulnerabilities met the criteria for inclusion in the cisa’s kev catalog. Vulncheck also named the top sources of exploitation evidence during the quarter. The disclosure of known exploited vulnerabilities was from 50. Automates it operationszero trust network accessenable frictionless work Learn how to use the kev. Shadowserver disclosed evidence of 31 actively exploited vulnerabilities, followed by. Vulnerability in best practical solutions, llc's request tracker v5.0.7, where the triple des (3des) cryptographic algorithm is used within smime code to encrypt s/mime emails. The flaws were added yesterday to cisa's 'known exploited vulnerabilities' (kev) catalog, with the broadcom brocade fabric os and commvault flaws not previously tagged as.CISA’s Known Exploited Vulnerabilities Catalog by David Vassallo
CISA Adds 6 Known Exploited Vulnerabilities to Catalog
Known Exploited Vulnerabilities Catalog 20220808.png Security
CISA's Catalog of Exploited Vulnerabilities BOD 2201
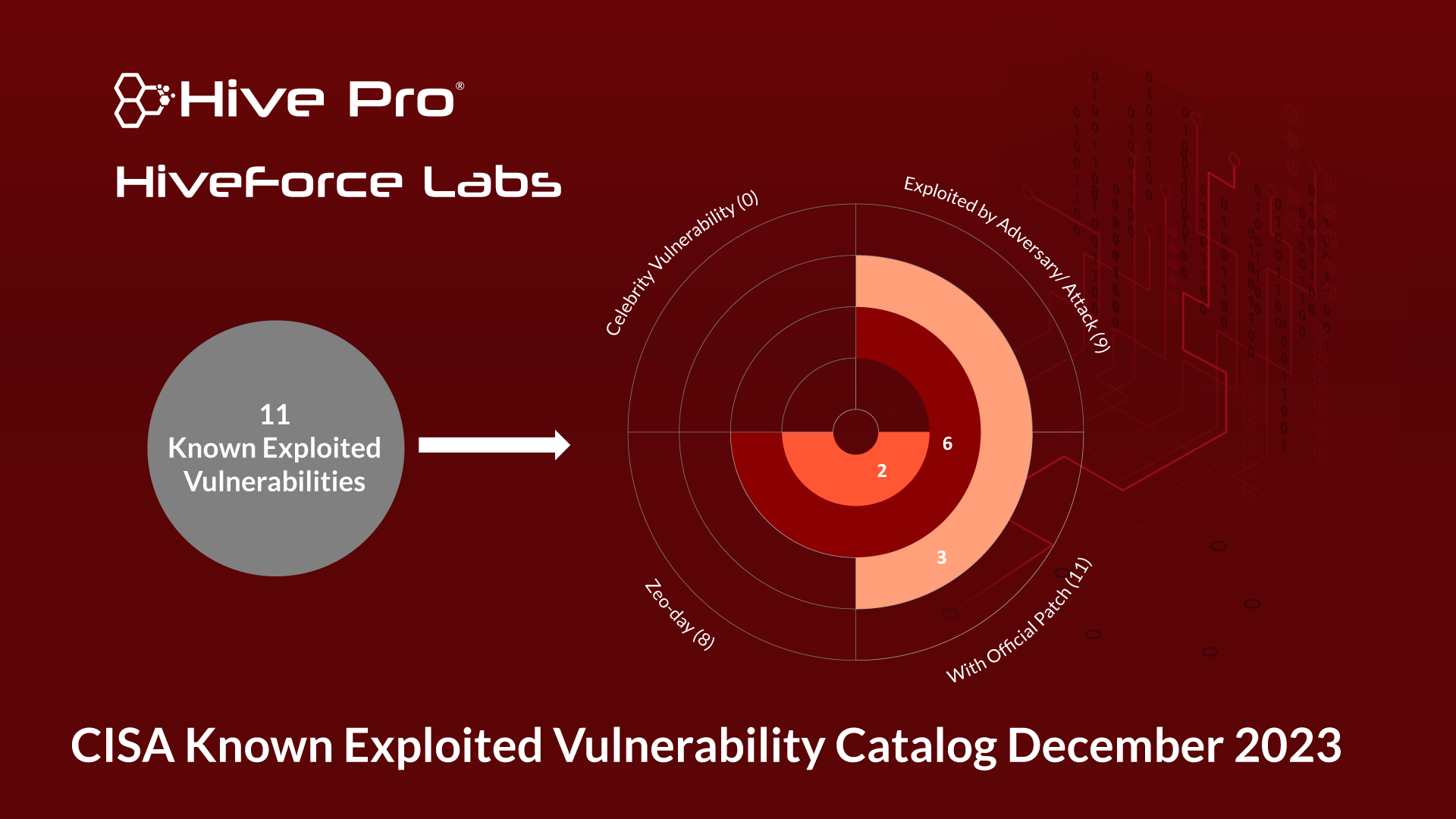
CISA's Known Exploited Vulnerability Catalog December 2023 HiveForce
Seven Known Exploited Vulnerabilities Added to CISA Catalog
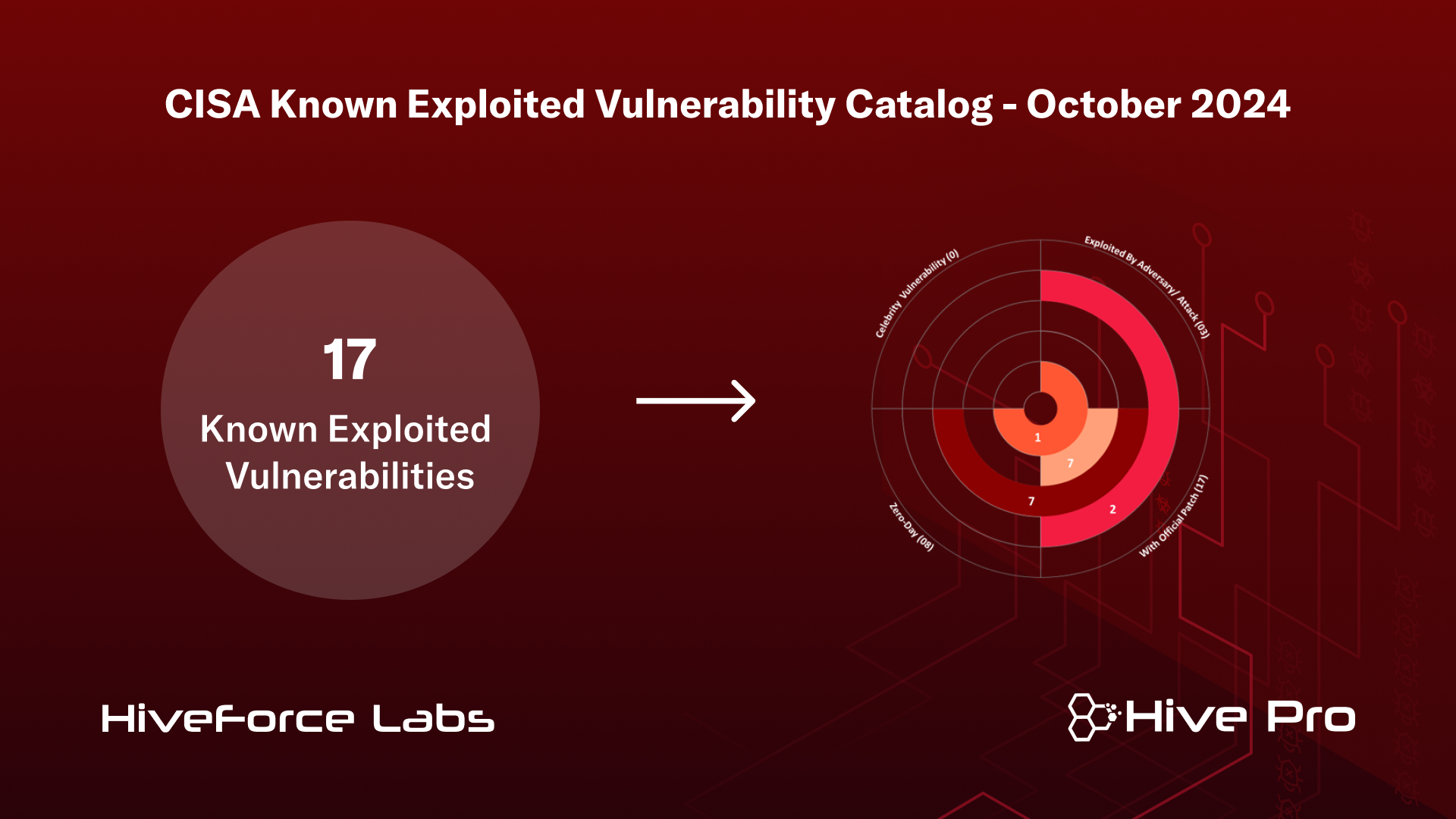
CISA's Known Exploited Vulnerability Catalog June 2024 HiveForce Labs
GitHub JosephTLucas/CISA_KNOWN_EXPLOITED_VULNERABILITIES_CATALOG Git
Known Exploited Vulnerabilities (KEV) Catalog By CISA
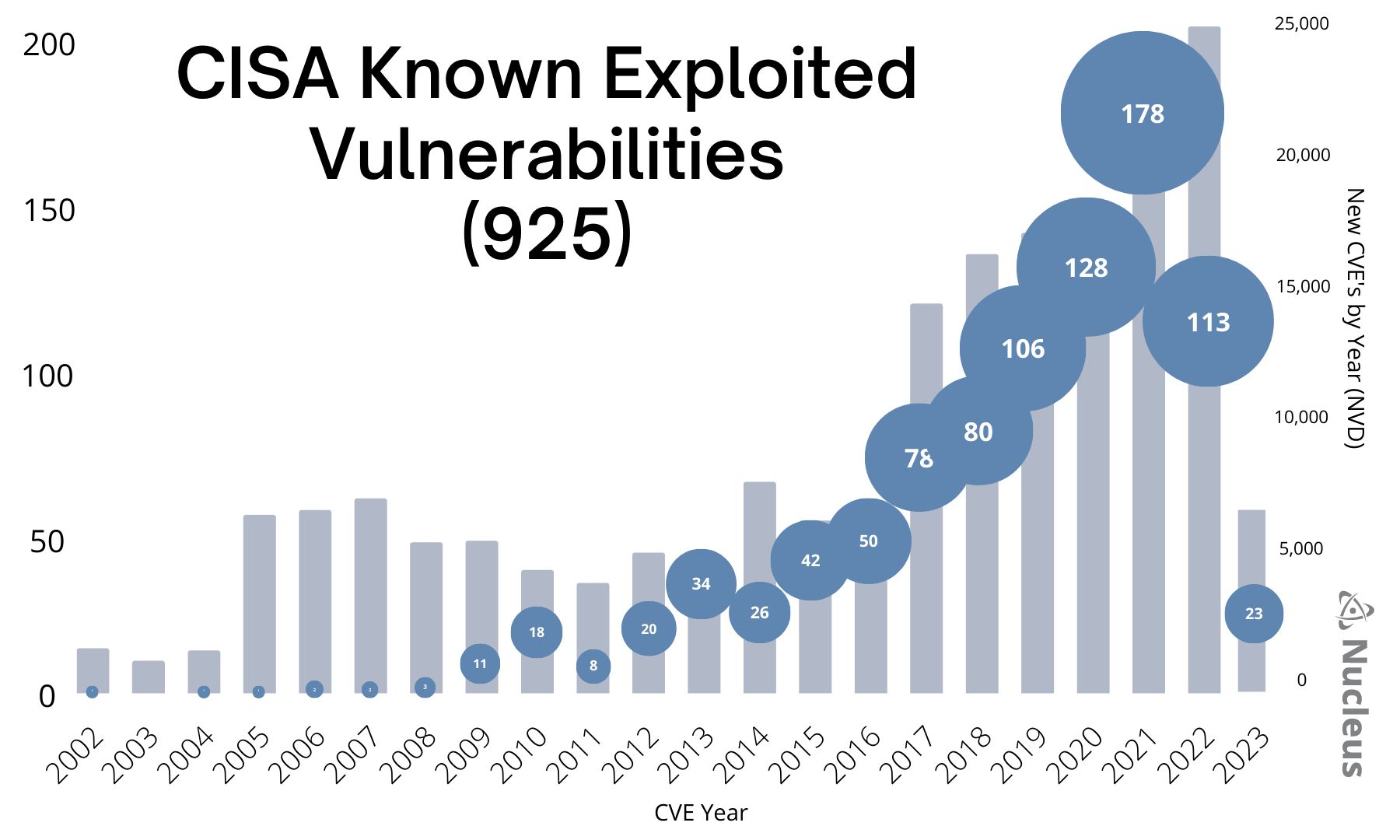
Analyzing 925 Known Exploited Vulnerabilities in the CISA KEV
Vuldb Provides Enhanced Details And Quality Of Cisa's Known Exploited Vulnerabilities Catalog (Kev), Which Contains Information About Security Issues That Have Been.
The Nvd Provides A Text Reference And A Hyperlink To The Kev Catalog For Cves That Appear In It.
In Q1 2025, Vulncheck Identified Evidence Of 159 Cves Publicly Disclosed For The First Time As Exploited In The Wild.
Cisa Maintains The Authoritative Source Of Vulnerabilities That Have Been Exploited In The Wild.
Related Post: