Cisa Kev Catalog
Cisa Kev Catalog - Cisa has added three new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. If cisa does not consider the information 100% accurate, cisa does not add the vulnerability to the kev catalog (however, cisa internally notes the vulnerability and will add it to the catalog should further exploitation evidence come to light that justifies its. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild: Cisa has added one new vulnerability to its known exploited vulnerabilities catalog, based on evidence of active exploitation. Organizations should use the kev catalog as an input to their vulnerability management prioritization. These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild. Providing an authoritative catalog is no trivial matter, and our team has developed three standardized criteria to identify which vulnerabilities to include in the kev. Available as csv and json files. The kev catalog, cpgs, and prni exemplify cisa’s commitment to fostering collaboration across public and private sectors. Available as csv and json files. If the information is reliable, cisa adds the vulnerability to the kev catalog; Cisa has added three new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. Organizations should use the kev catalog as an input to their vulnerability management prioritization. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild. If cisa does not consider the information 100% accurate, cisa does not add the vulnerability to the kev catalog (however, cisa internally notes the vulnerability and will add it to the catalog should further exploitation evidence come to light that justifies its. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited vulnerabilities. Providing an authoritative catalog is no trivial matter, and our team has developed three standardized criteria to identify which vulnerabilities to include in the kev. Cisa will continue to add vulnerabilities to the catalog that meet the specified criteria. These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. If the information is reliable, cisa adds the vulnerability to the kev catalog; Organizations should use the kev catalog as an input to their vulnerability management prioritization. Cisa will continue to add vulnerabilities to the catalog that meet the specified criteria. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited. If cisa does not consider the information 100% accurate, cisa does not add the vulnerability to the kev catalog (however, cisa internally notes the vulnerability and will add it to the catalog should further exploitation evidence come to light that justifies its. These initiatives have helped to reshape cybersecurity by prioritizing proactive defense, measurable outcomes, and. Available as csv and. The known exploited vulnerability (kev) catalog. These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Available as csv and json files. Cisa will continue to add vulnerabilities to the catalog that meet the specified criteria. Cisa has added one new vulnerability to its known exploited vulnerabilities catalog, based on. Cisa has added three new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. The kev catalog, cpgs, and prni exemplify cisa’s commitment to fostering collaboration across public and private sectors. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited vulnerabilities. Organizations should use the kev. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild: Cisa has added four new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. Available as csv and json files.. The known exploited vulnerability (kev) catalog. If cisa does not consider the information 100% accurate, cisa does not add the vulnerability to the kev catalog (however, cisa internally notes the vulnerability and will add it to the catalog should further exploitation evidence come to light that justifies its. These initiatives have helped to reshape cybersecurity by prioritizing proactive defense, measurable. The kev catalog, cpgs, and prni exemplify cisa’s commitment to fostering collaboration across public and private sectors. Available as csv and json files. These initiatives have helped to reshape cybersecurity by prioritizing proactive defense, measurable outcomes, and. Cisa has added three new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. The known exploited vulnerability (kev). These initiatives have helped to reshape cybersecurity by prioritizing proactive defense, measurable outcomes, and. Cisa has added four new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. Cisa will continue to add vulnerabilities to the catalog that meet the specified criteria. If cisa does not consider the information 100% accurate, cisa does not add the. Providing an authoritative catalog is no trivial matter, and our team has developed three standardized criteria to identify which vulnerabilities to include in the kev. These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Organizations should use the kev catalog as an input to their vulnerability management prioritization. The. These initiatives have helped to reshape cybersecurity by prioritizing proactive defense, measurable outcomes, and. The known exploited vulnerability (kev) catalog. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild. Cisa has added four. Providing an authoritative catalog is no trivial matter, and our team has developed three standardized criteria to identify which vulnerabilities to include in the kev. Cisa has added four new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. Available as csv and json files. If cisa does not consider the information 100% accurate, cisa does not add the vulnerability to the kev catalog (however, cisa internally notes the vulnerability and will add it to the catalog should further exploitation evidence come to light that justifies its. If the information is reliable, cisa adds the vulnerability to the kev catalog; These initiatives have helped to reshape cybersecurity by prioritizing proactive defense, measurable outcomes, and. These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited vulnerabilities. Cisa has added one new vulnerability to its known exploited vulnerabilities catalog, based on evidence of active exploitation. Cisa will continue to add vulnerabilities to the catalog that meet the specified criteria. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild: Organizations should use the kev catalog as an input to their vulnerability management prioritization.CISA’s Greene details focus on strengthening cybersecurity resilience
CISA KEV Blogs Stay tuned with latest updates and findings in cyber
Understanding and Addressing the Challenges of CISA's KEV Catalog
CISA's Known Exploited Vulnerability Catalog June 2024 HiveForce Labs
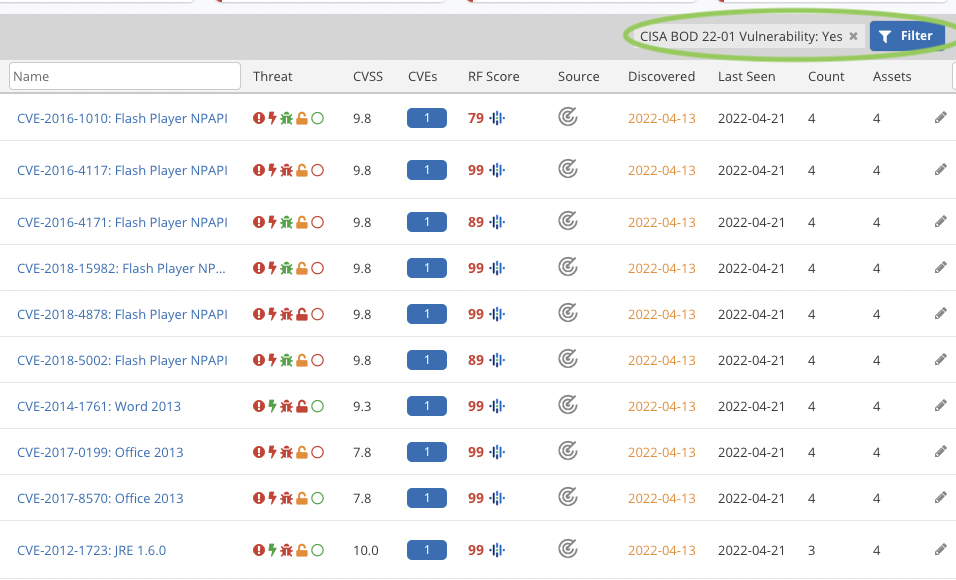
Nucleus Use Case CISA KEV Vulnerability Prioritization
Using the CISA Kev Catalog FOSSA
CISA KEV Catalog Update Part III March 2025
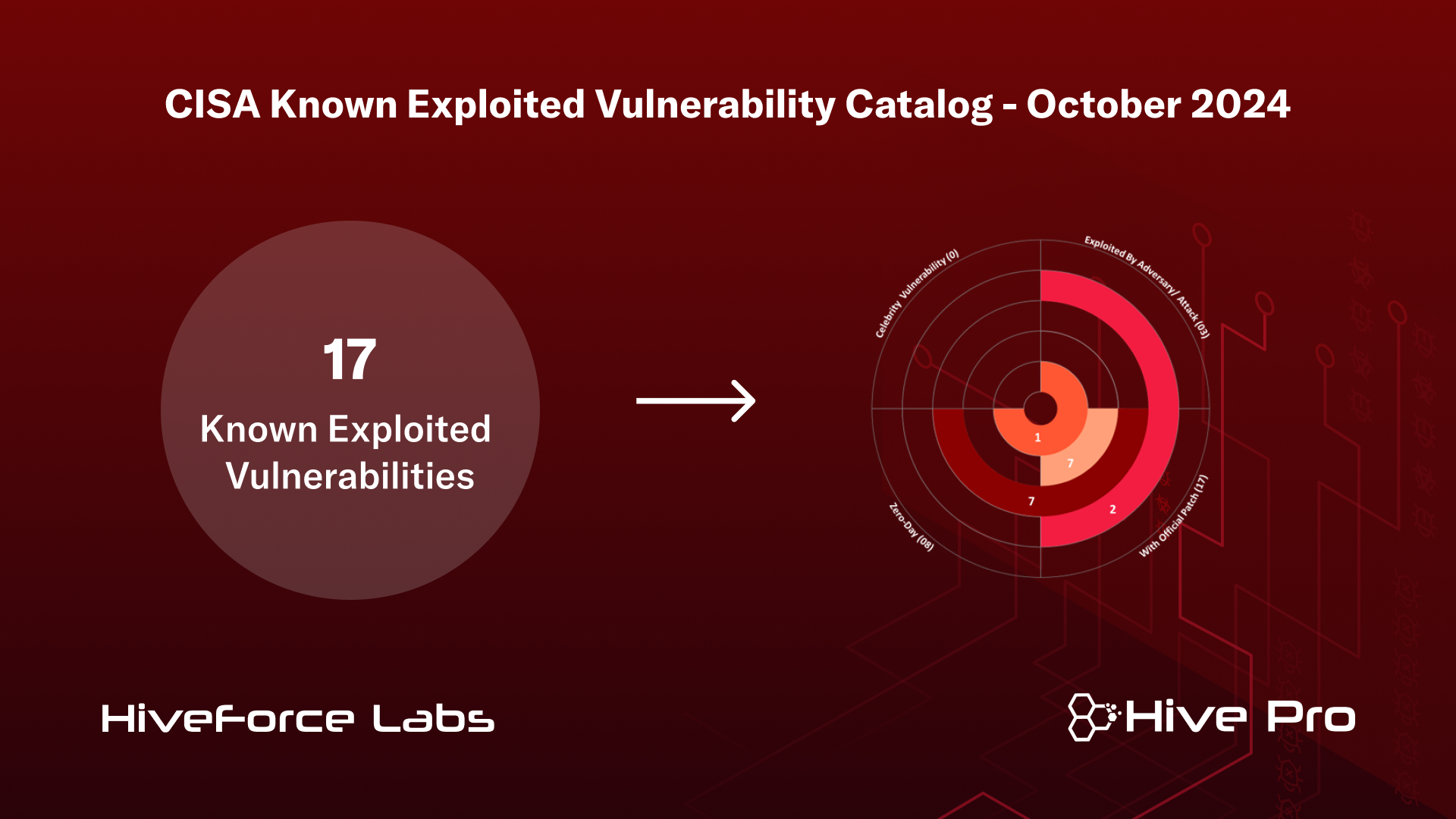
CISA KEV Catalog Update Part IV October 2024
Bitsight A Global View of Cisa Kev Catalog PDF Vulnerability
MITRE Mapping of CISA KEVs and its Challenges
For The Benefit Of The Cybersecurity Community And Network Defenders—And To Help Every Organization Better Manage Vulnerabilities And Keep Pace With Threat Activity—Cisa Maintains The Authoritative Source Of Vulnerabilities That Have Been Exploited In The Wild.
The Kev Catalog, Cpgs, And Prni Exemplify Cisa’s Commitment To Fostering Collaboration Across Public And Private Sectors.
Cisa Has Added Three New Vulnerabilities To Its Known Exploited Vulnerabilities Catalog, Based On Evidence Of Active Exploitation.
The Known Exploited Vulnerability (Kev) Catalog.
Related Post:





.png)